In the CSA’s forensic lab, agents dissecting cyberattacks use sophisticated gadgets and race against time
“The schedule was very tight and we were racing against the clock; everyone was looking for answers quickly to solve the problem,” said Mr. Ryan Chen, 36, a senior consultant with CSA who coordinated operations between different teams during the investigation.
“We also had to provide timely information to the media and members of the public. The investigation team had to provide the daily update to the stakeholders, even before the commission of inquiry.
“They also had to make sure the full report was very detailed and accurate because this was a very serious issue. It was quite a stressful time for our guys.”
CYBER-DETECTIVES
Much like police officers, CSA officers must go to the scene of the “crime”, collect evidence and process it, then determine the root cause of the incident, the intent of the attacker and whether any data was stolen.
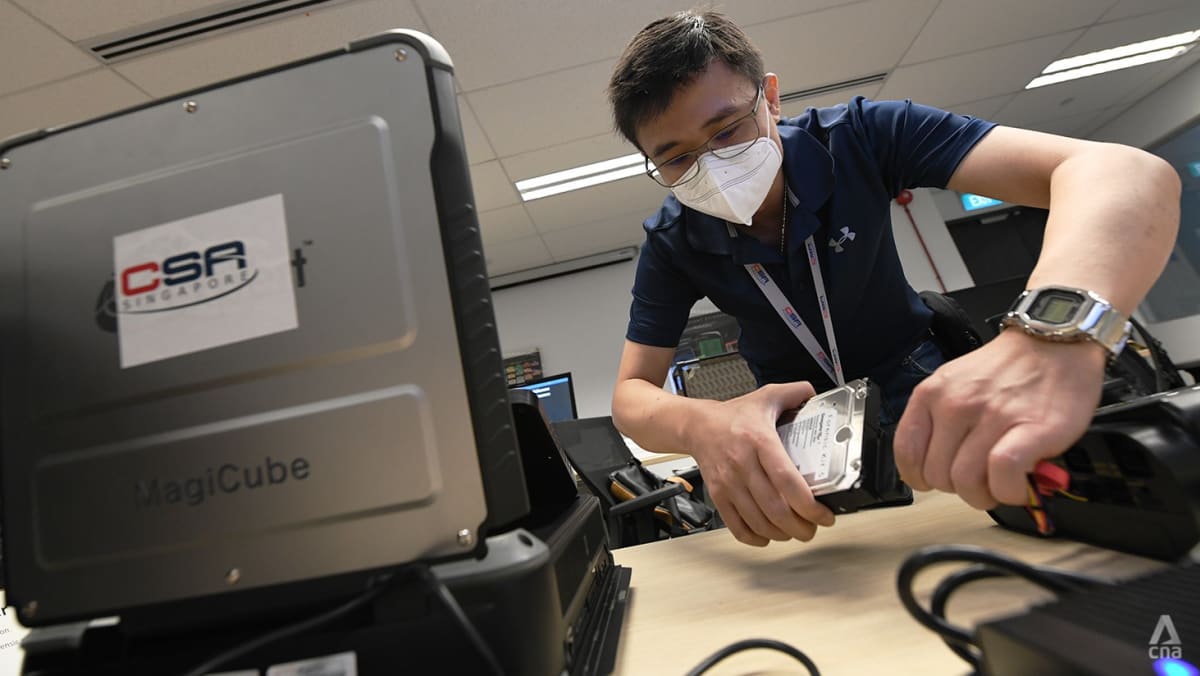
CSA agents also use specialized equipment to extract and copy data from storage devices, which allows them to analyze the threat, check system vulnerabilities and recommend preventive actions.
If an attack is in progress, as was the case with the SingHealth breach, the priority is to prevent the attacker from gaining access to the system and closing other potential backdoors that could be exploited.
Mr. Chen said CSA’s primary role during the 10 days was to help contain the cyberattack, reconstruct the attack’s timeline and assess its impact, including what data was stolen and whether records have been modified or deleted.
There has also been “pressure” on authorities to quickly notify data subjects whose data may have been stolen, he said.
“We were dealing with a skilled and sophisticated threat actor who was also very persistent and resourced,” he added.

Comments are closed.